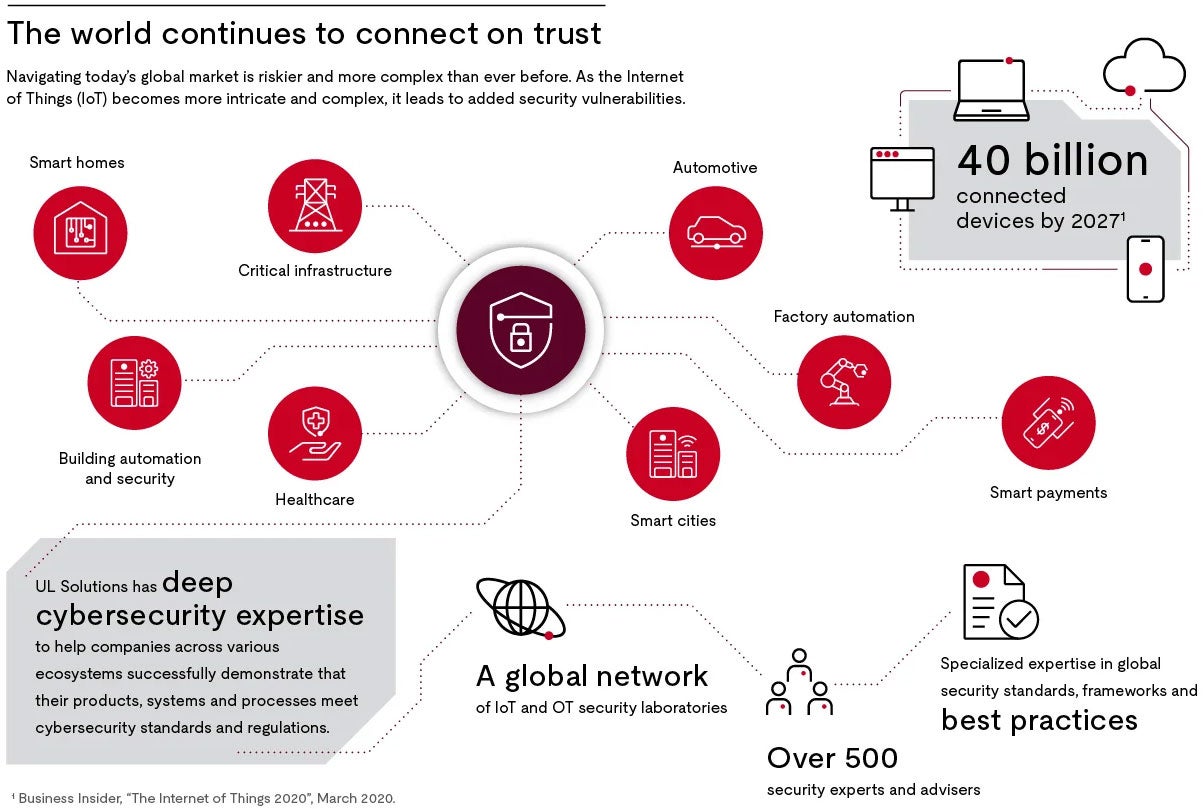
Building cybersecurity into connected products is a critical component needed to unlock the vast potential of IoT and OT innovation. If done well, it empowers companies to successfully implement their business strategy, mitigate risks, protect their brand reputation, create product differentiation and establish market leadership.
Related resources
Guide to the Cyber Resilience Act
Learn more about the European Cyber Resilience Act (CRA) that aims to enhance the cybersecurity of products with digital elements sold within the EU.
Connections and relationships between CRA stakeholders
The Cyber Resilience Act impacts various stakeholders within the cybersecurity ecosystem. Learn more about how these stakeholders interact.
Advancing cybersecurity capabilities
Even with the advancement of connected product innovation across industries, most products today are still built to functional, cost and time-to-market objectives. Security may not be a primary consideration and the regulatory environment may often be fragmented and not required. This can unfortunately lead to compromised data and subsequent loss of stakeholder trust. To mitigate organizational risk, security needs to be a consistent and thorough consideration throughout product development and lifecycle management processes.
Many organizations are looking to advance their IoT and OT cybersecurity capabilities and asking:
- How can we best incorporate security as part of our connected products or systems?
- How can we help educate our development and security teams so they incorporate security by design principles into product design and development?
- How can we evaluate the maturity of our security and development processes?
- How can we ensure secure product lifecycle management (managing security throughout device lifecycle)?
- How can we demonstrate our cybersecurity posture to the marketplace?
Get in touch
Have questions, need specifics? Let's get this conversation started.